
BLOG

BLOG
Every week we bring you various compliance checks like PCI-DSS, HIPAA, ISO 27001 and SOX so as to make our readers aware of the various checklists that businesses need to follow in order to be compliant with it. Today we will discuss about FISMA.
FISMA stands for the Federal Information Security Management Act (FISMA). It was signed into law part of the Electronic Government Act of 2002. This act is required for the federal agencies to develop, document, and implement an information security management program for giving safeguard to their information systems which even includes those who are provided or managed by another agency, contractor, or third party.
FISMA was created in order to enable all the federal agencies to be able to create and fully implement a thorough information security plan and safeguard their operations. FISMA comes under larger legislation known as the E-Government Act which aims at uplifting the awareness regarding the necessity of cybersecurity and its impact on the assets of the country.
Under the Federal Information Security Modernization Act, FISMA was amended by the congress in 2014. This amendment modified FISMA based on current security concerns. It also asked the federal agencies to implement stronger measures in terms of security and pay more attention to regulatory compliances.
When it was initially announced, FISMA applied only to the federal agencies. But with time, the law has gradually incorporated state agencies like insurance, Medicare, and Medicaid also. Moreover, companies who work with federal agencies are also obliged to follow FISMA. So, the private sectors companies must adhere to these guidelines in order to get contracts from federal agencies.
Must Read- Glance At The United States Cyber Security Laws
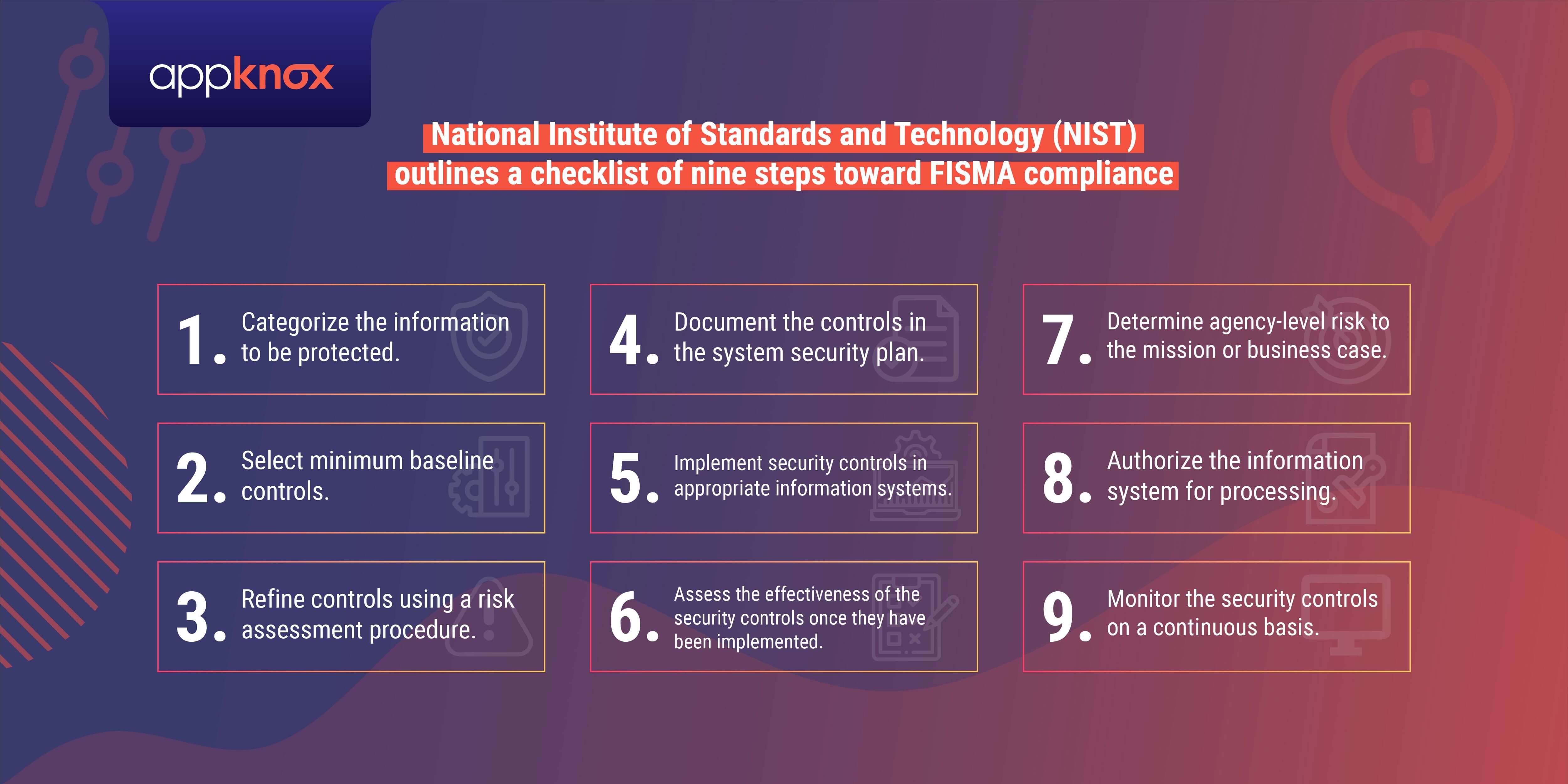
The National Institute of Standards and Technology (NIST) and the Office of Management and Budget (OMB) are assigned specific responsibilities by FISMA in order to strengthen information security systems. The head of each agency is required to implement policies and procedures to cost-effectively reduce information technology security risks to an acceptable level.
NIST is responsible for developing standards, guidelines, and associated methods and techniques for providing adequate information security for all agency operations and assets, excluding national security systems. NIST works closely with federal agencies to improve their understanding and implementation of FISMA to protect their information and information systems and publishes standards and guidelines which provide the foundation for strong information security programs at agencies.
Good Read: What is NIST Cybersecurity Framework? ( CSF )
This program’s main objective is to ensure that the core information security principles namely confidentiality, integrity, authenticity, non-repudiation and availability of information and information systems are provided. The key elements of the program can be summarized as below:
This ensures that the right officials are assigned security responsibilities.
This includes the risk and consequent impact on the agency and would eventually result from the unauthorized access, disclosure, use, disruption, destruction or modification of information and information systems supporting an agency’s operations and assets.
The policies and procedures are being made to reduce the risks and to ensure that the security of information is addressed throughout the life cycle of each organizational information system in a properly documented manner and this type of procedures include detecting, responding, reporting to security incidents and procedures to ensure continuity of operations.
All the personnel including the contractors are required to be trained in regards to information security principles and the security risks related to their job requirements, and an agency’s policies and procedures.
The test should be done annually after some days that the effectiveness of information security policies, procedures, practices.
A Process for Planning, Implementing, Evaluating, and Documenting Remedial Actions: It also has a process for addressing any deficiencies that might occur in the information security policies, procedures, and practices of the organization which needs to be implemented and documented by the agency.
Enterprises have developed a fatalistic attitude towards compliance. They believe that chasing compliance might divert their time and resources from achieving optimum business efficiency.
Being compliant with the FISMA guidelines ensures that the agency's data security issues are covered. Moreover, it also ensures the safety of user data and substantially reduces IT-related costs as well. But, adapting FISMA compliance is a must to unleash several business benefits mentioned below:
FISMA compliance assures that the federal agencies and related organizations develop and implement a data security program incorporating regular scanning, monitoring, and updating all cybersecurity policies. Implementing a threat monitoring program for all systems and assets assures establishing a robust patch management system and highlights all cyber vulnerabilities real-time. Along with this, it helps in resource allocation to combat evolving threats.
Unaware human assets with a lack of proper training are the softest target for cyber attackers. FISMA addresses the issue of inadequate problems by requiring all federal agencies and related organizations to implement and develop an ongoing data security training program. Adding a dedicated information security training program enables businesses to create a sufficiently strong organizational culture and cybersecurity posture.
The core of FISMA is the implementation and development of a risk-management centred approach to data security. Using the FISMA model, businesses unveil the looming threats, making vital operational decisions regarding their risk appetite.
With FISMA compliance, organizations can create a stout framework for a long-lasting data security program that is flexible to adapt to current and future threats.
FISMA explicitly necessitates organizations to create and implement a well-planned incident response program. Threat detection and mitigation techniques strengthen the security posture of organizations, creating a comprehensive cybersecurity program. Designing and implementing an incident response plan makes organizations more resilient towards probable cyber threats.
If anyone fails a FISMA inspection, then it might have the following negative consequences:
There are many who can help federal agencies with all the requirements mandated by FISMA compliance.
The gap analysis of them is to help review the agency information security program and then identify it for the deficiencies and gaps that prevent the agency from achieving compliance.
Enterprise Risk Management (ERM can provide support and guidance for the implementation of the information security program including the following key components:
To be FISMA compliant, enterprises need to update stringent data security controls organization-wide, guided by the NIST framework:

Hackers never rest. Neither should your security!
Stay ahead of emerging threats, vulnerabilities, and best practices in mobile app security—delivered straight to your inbox.
![]() Exclusive insights. Zero fluff. Absolute security.
Exclusive insights. Zero fluff. Absolute security.
![]() Join the Appknox Security Insider Newsletter!
Join the Appknox Security Insider Newsletter!
