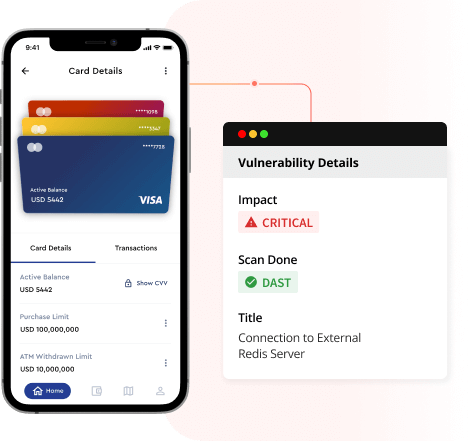
Automated real-time DAST to evaluate mobile app security on real devices
Assess the security posture of your mobile application while it is running in its operational environment.
Interact remotely with your app and get real-
time scan results
-
Test on Real Devices
-
Schedule Scans
-
Uncover Vulnerabilities
-
Customize Reports
Understand data flow seamlessly
Effortlessly replicate genuine app interactions with remote access. Grasp comprehensive insights into the 'what, when, where & how' of information sharing through your app, identifying potential security vulnerabilities.
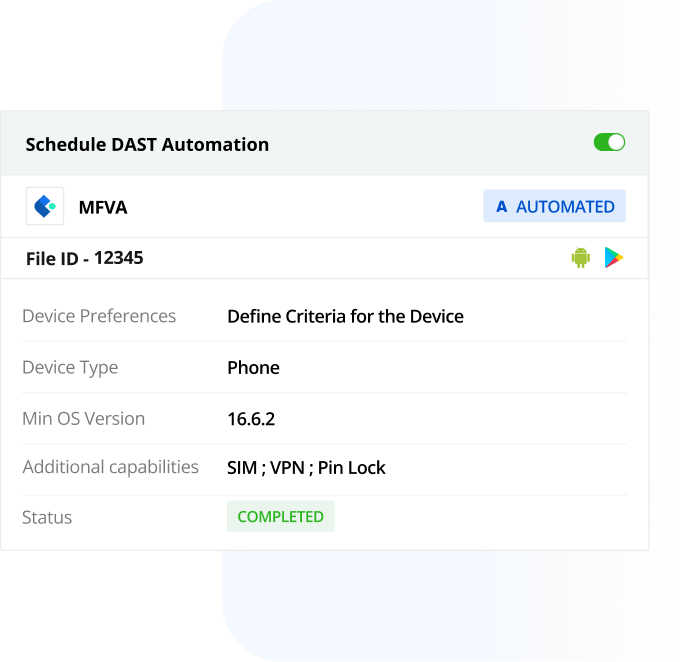
Simplify security management for multiple apps
Experience simplified security for multiple apps with Appknox's DAST scan automation. Schedule future scans effortlessly with a quick, one-time setup process within a minute.
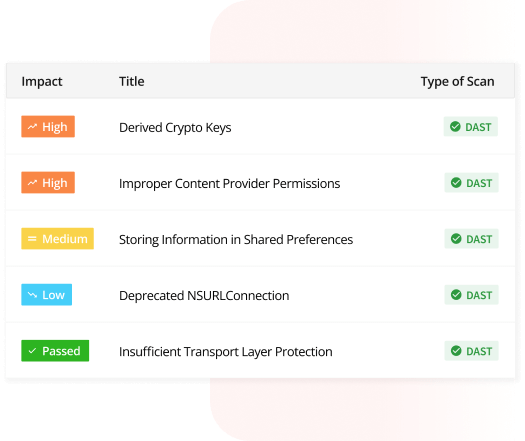
Leverage the extensive coverage of test cases
Quickly identify vulnerabilities that could impact your business's financial standing and brand reputation with multiple test cases dedicated to the dynamic security scan.
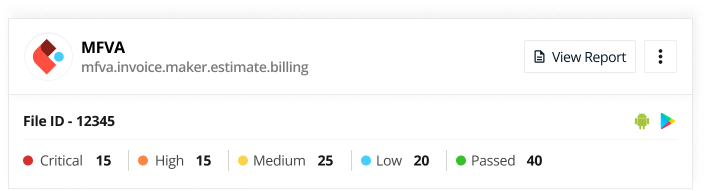
Generate tailored reports that align with your compliance needs
Get a detailed analysis of the severity of vulnerabilities and their potential threats. Customize impact indicators based on your organization's priorities and business goals.

Get real-time vulnerability analysis scans with Appknox VA
Experience testing coverage that extends beyond emulators. Initiate Appknox DAST to seamlessly scan your mobile app on real devices remotely. Enable a timely mitigation response to new security threats.
DAST Scan
by Appknox
Automated DAST Running
Download DAST Reports
types of scan reports.
Easy and Quick
Address the needs of your entire DevSecOps team
CISO
Ensure organization-wide security and compliance with continuous visibility into the security posture with proactive threat detection.
Head of Engineering
Empowers you to deliver high-quality secure applications within deadlines by helping development teams address security issues promptly with real-device testing.
Security Researcher
Discover and analyze emerging security threats and vulnerabilities by automating security scans on real devices with realistic attack scenarios for accurate identification.
DevOps Manager
Streamlines development, testing, and deployment processes by automating security testing in CI/CD pipeline with integrated real-device testing.
Solution Architect
Helps you design and implement secure, scalable, and efficient software architectures by validating proposed architecture security with in-depth reports and analysis.
Developer
Ensures efficient and secure code development by fixing code vulnerabilities without disruption in workflow.
Still curious about DAST
Uncover its value proposition for your business through these dedicated resources.
Dynamic Application Security Testing (DAST): An Overview
Dynamic Application Security Testing (DAST) is an advanced testing method that tests the production environment and analyzes application security at runtime
Know more ▶Revolutionizing Security Testing: Advancements...
With organizations continuing to build and enhance their mobile applications and developers embracing new ways of building
Know more ▶Built for Mobiles: Why Choose a Mobile-First Vulnerability...
Security teams spend an average of 130 hours per week monitoring and tracking threats...
Know more ▶Appknox gives us quick, step-by-step framework to resolve vulnerabilities. We've been effectively managing the security assessment of our entire mobile app ecosystem.
Johnathan Black
CEO at Singapore Airline