The ecosystem of cybersecurity gets complicated day-by-day as hackers continue to push their boundaries of motivation and innovation. Correspondingly, those at stake can't continue with the age-old approach and measures must be taken to break the barriers of the traditional security methods. Here we have briefed 10 areas outlined in a PwC whitepaper, where a change in mindset and approach towards cybersecurity could bring astonishing results for your business.
Why Your Approach to Cybersecurity Needs to Change?
In recent times, the never-ending series of devastating cyber-attacks have forced the business leaders to rethink their attitude towards cybersecurity. In 2017, more records were stolen just in the first six months than all of 2016. Attacks like 'NotPetya' launched to target the IT structure of businesses compel us to rise to this challenge and repurpose resources to fight these rising cyber threats, the leading concern for UK and US CEOs according to the PwC's global CEO survey.
Ten important cybersecurity challenges that needs to be faced
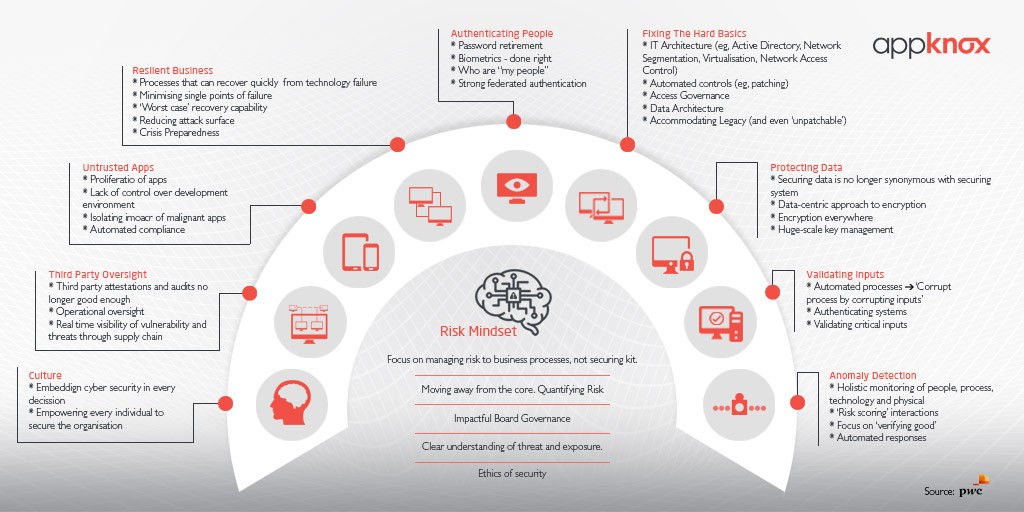
Organisations need to take a strategic decision to move beyond good practice security controls. In addition to this, they must now identify how they need to change their operations. The research paper believes that the cybersecurity challenges to be faced can be roughly divided into 10 groups. There is no one-size-fits- all solution and different organisations will need to emphasise different areas. To confront the following challenges, organisations will have to change the way they think, work and behave.
Importantly these challenges will not be static, new problems will continue to appear as attackers advance their techniques.
1) Authenticating people
One common feature of almost every cybersecurity attack is exploitation of static passwords. The need to move beyond static passwords has been recognised for a long time, but action is now required. One-time passwords, two-factor authentication, biometrics and continuous authentication using artificial intelligence to monitor behavioural patterns are all possible alternatives - but static passwords are still predominant method for authenticating individuals today.
2) Fixing the hard basics
The fact that so many security breaches are made possible by one of a small number of basic security failures seem to imply security should be relatively straightforward to improve. However, the challenge for many organisations, especially larger groups or those with legacy IT estates, is that fixing the basics is hard, and often it cannot be addressed effectively by traditional means.
Examples of these basic issues include:
- The consistent application of security practices
- The question of what systems and applications connect to a network
- Who has access to what systems and data
- How data is managed
- How a global organisation is segmented to prevent attacks from spreading
To address these questions effectively requires new ways of thinking and new architectures.
3) Protecting data
In today's world, an organisation's data flows across many systems - the vast majority of which are outside the control of the organisation. Cloud service providers, suppliers, partners, staff and even customers operate systems on which sensitive data is stored and processed.
The challenge now is how to secure the data when you have little or no control of the systems on which the data is stored or processed. The whitepaper suggests a different approach to encryption and the management of encryption keys. Data must be encrypted so that wherever the data goes, the originator of the data retains control of the keys and can determine, at a granular level, whether access to that data is granted or denied.
4) Validating inputs
Increasingly, cyber attacks are based on a concept that requires defenders to think more broadly about what cybersecurity is in order to manage them. Innovative attackers targeting a particular process or system may not attack that system directly, but may instead seek to corrupt a process by corrupting its inputs.
One example of the above scenario is - stealing money from a bank's systems by corrupting the customer inputs to online banking through online banking Trojans.
Defending against the above types of attacks requires digital processes to be designed with input validation at their core - for example: verifying sources of data, verifying the integrity of data, comparing inputs from different sources, and using artificial intelligence to monitor for deviations in data patterns.
5) Anomaly detection
Conventional approaches to security monitoring have focused on finding known bad activity. Anti-virus software, intrusion detection systems and sandboxes are examples of monitoring controls that are built around finding known, identifiable threats.
However the proliferation of attacks and the ability of attackers to craft custom malicious code for a single target mean that this approach is not sustainable.
The whitepaper suggests making use of artificial intelligence and machine learning tools to effectively identify and block attacks that have not been seen previously. This will thus enable new attack types to be blocked in real-time, without the need for human intervention, which is critical for combatting attacks such as NotPetya, which achieved it's destructive intent within minutes.
6) Culture
Cybersecurity impacts every area of a business and its operations, and requires organisations to consider changing how they operate as much as applying security controls - they must embed cybersecurity into their DNA.
The PwC research highlights two things for this:
- Firstly, every individual in the organisation needs to believe that they have a responsibility to protect the organisation through the way they do their job. They need to be supported and rewarded for doing so and empowered to challenge processes, decisions or situations that may put the organisation at risk.
- Secondly, every decision made within an organisation should consider cybersecurity implications. This starts from right at the top, with executive management and the board realising that almost every decision they make can impact cyber risk - examples include entering new markets, releasing new products, M&A activity, interacting with customers in a new way and even taking on new customers.
7) Third party oversight
The whitepaper highlights that the cyber risks in supply chains that are increasingly apparent in recent years, and along with rises the need to take action in order to manage that risk.
The research provides three elements to the action that is required to manage risk through the supply chain:
- The first step is often overlooked and that is simplify the problem by simplifying the supply chain. Reducing the number of suppliers that have access to systems will enhance security.
- The second step is to streamline and optimise the audit and review activity undertaken over suppliers.
- The third step for organisations is to develop a real-time operational view of threats and vulnerabilities through their supply chain.
8) Untrusted apps
Often the risks presented by applications are a result of errors in coding and poor software development practices. With a proliferation of applications and a reliance on methods for application development in the cloud such as DevOps, organisations will need to invest significantly to ensure both rigour in their software development and that software is reviewed for errors that could be exploited by an attacker.

To generate further awareness that many popular mobile apps built today are plagued by security issues and vulnerabilities, we conducted our own in-house research showcasing the security trends in the top 50 mobile apps in the shopping category in the US. Our findings show that over 84% of the apps analyzed have more than three high-level vulnerabilities in them.
9) Resilient business
It is now an accepted truth that cyber breaches will happen. Many businesses are therefore focusing on how they could be resilient to different types of successful cyber-attack and minimise impact.
The need of the hour is for different thinking around what is required to construct a resilient business. Some examples of this include:
- Understanding and minimising single points of failure due to reliance on a single technology or provider
- 'Worst case' recovery capability
- Reducing attack surface
- Preparedness for a 'cyber crisis'
10) Risk mindset
The nine previous challenges collectively speak to an underlying issue that is confronted by this whitepaper - how do we change the mindset around what cyber risk is and what is needed to manage it?
The following can be helpful in answering the above questions:
- Managing the risk from cyber attacks requires a deep understanding of what digital processes and data flows the business is built on, their reliance on others, their inputs, and their dependencies.
- Clear understanding of potential threats and exposures
- Impactful board governance will ensure cybersecurity is not just a programme but a driver of business and technology re-architecture, supported by metrics that quantify risks.
- Answering ethical questions in line with clear organisation values. Example - questions such as what should be monitored and what should deliberately be placed outside the reach of any monitoring capability etc.
Final Thoughts
Last but not the least, facing the challenges and rethinking your approach to cybersecurity as outlined in this whitepaper will require change and commitment. That can only be possible whe the risk mindset of an organisation reflects the reality that cybersecurity is as much about re-architecting business and technology as it is about applying security controls.


.jpg?width=64&height=64&name=10606600_10204086667262761_7381430219125488912_n%20(1).jpg)













_HighPerformer_HighPerformer.png?width=123&height=160&name=DynamicApplicationSecurityTesting(DAST)_HighPerformer_HighPerformer.png)
_BestEstimatedROI_Roi.png?width=123&height=160&name=StaticApplicationSecurityTesting(SAST)_BestEstimatedROI_Roi.png)

